Executive Summary
DrugHub Market functions as a decentralized hidden service operating exclusively within the Tor network. Engineered as an anonymous commercial platform, it facilitates peer-to-peer exchanges of digital and physical commodities through heavily encrypted channels.
Since its inception, the platform has distinguished itself by rejecting older, vulnerable protocols in favor of a modernized stack. By strictly utilizing Monero (XMR) to obfuscate financial trails and enforcing native PGP (Pretty Good Privacy) for all communications, the architecture is designed to minimize metadata leakage.
Independent researchers note that the system operates on a rigorous, utilitarian philosophy—eschewing complex, script-heavy user interfaces in favor of lightweight, static delivery mechanisms that reduce the attack surface for potential adversaries.
Core Attributes
- Network: Tor Hidden Service
- Currency: Monero (XMR) Only
- Security: Enforced PGP, 2FA
- Funding: Walletless / Direct Pay
- Design: Static, JS-Independent
Technical Architecture
Cryptographic Enforcement
The infrastructure mandates end-to-end PGP encryption. All addresses and sensitive operational communications bypass the server's plaintext memory, remaining indecipherable to administrative nodes.
Walletless Financial Routing
Centralized wallets have been eliminated. The system utilizes per-transaction XMR addresses (Walletless mode) combined with multisignature escrow, ensuring funds are never stockpiled centrally.
Anti-DDoS Isolation
A strict routing matrix acts as a barrier before the core server is reached. End-users must solve cryptographic challenges to receive dedicated session tokens, filtering out automated botnet traffic.
Platform Interface Preview
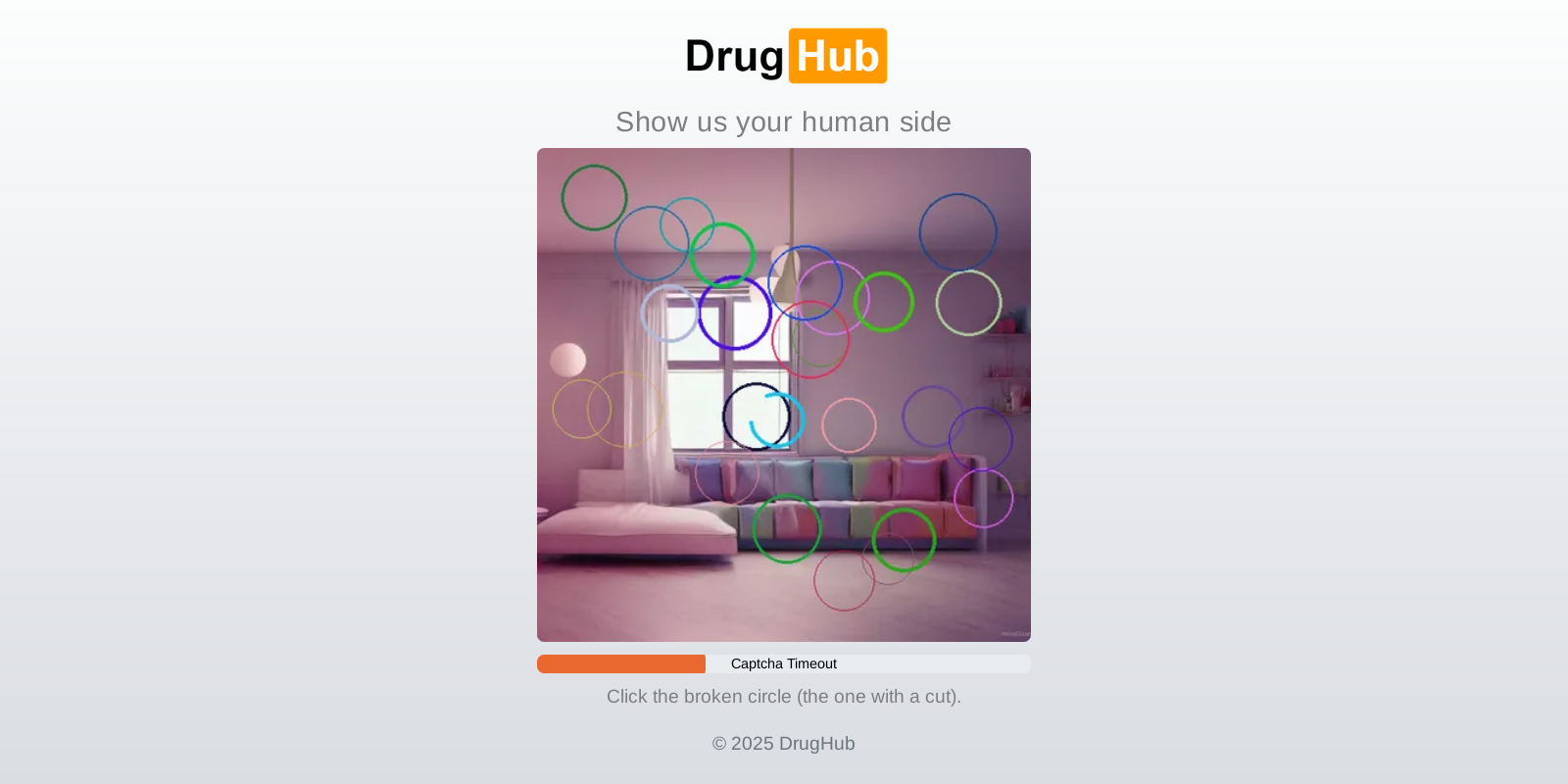
Fig 1. DDoS Protection Screen
Initial routing layer analysis shielding the main server infrastructure.
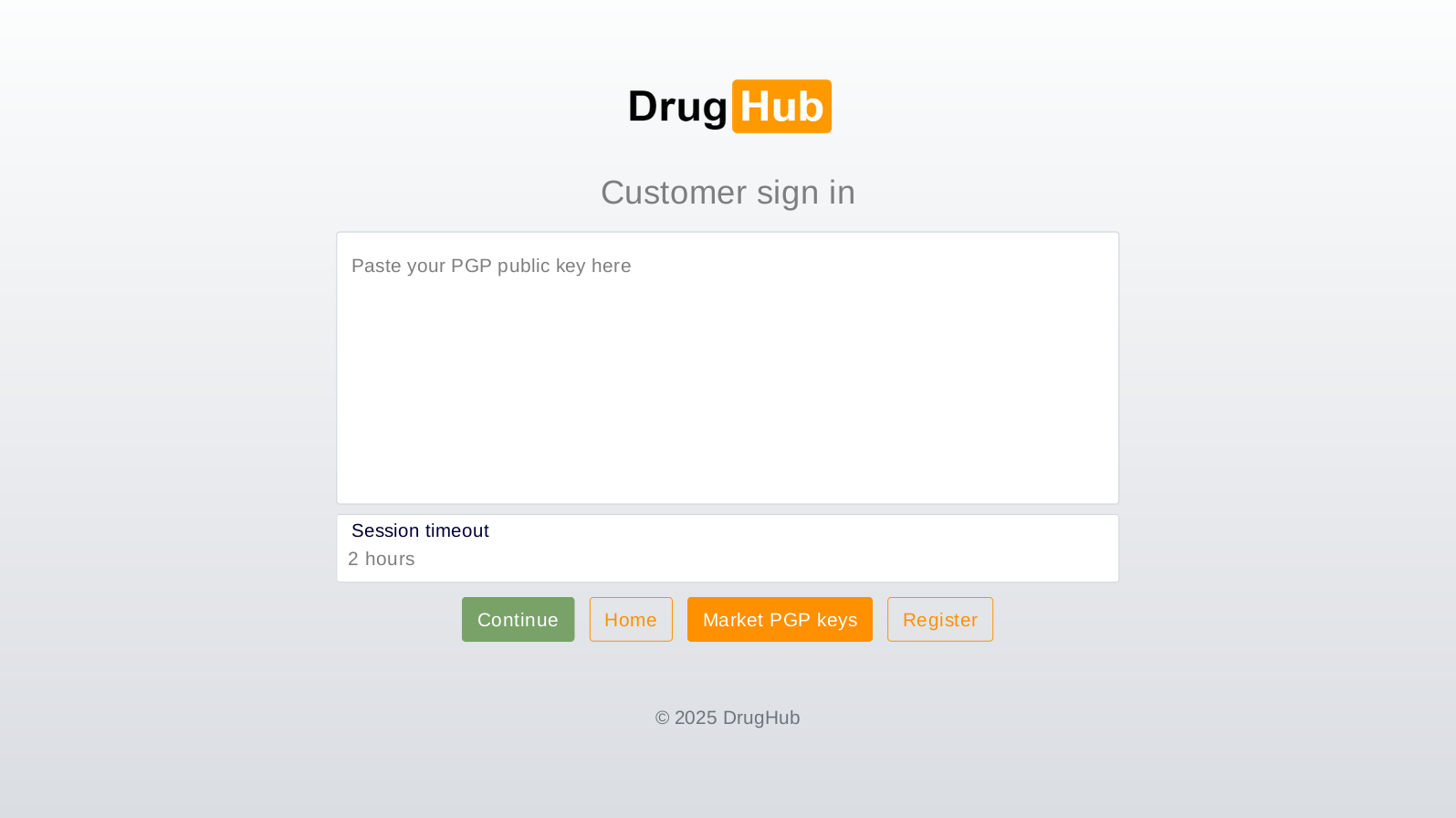
Fig 2. User Login Interface
Observation of the multi-stage authentication sequence.
Fig 3. Account Registration Page
Data collection points and mandatory cryptography key generation.
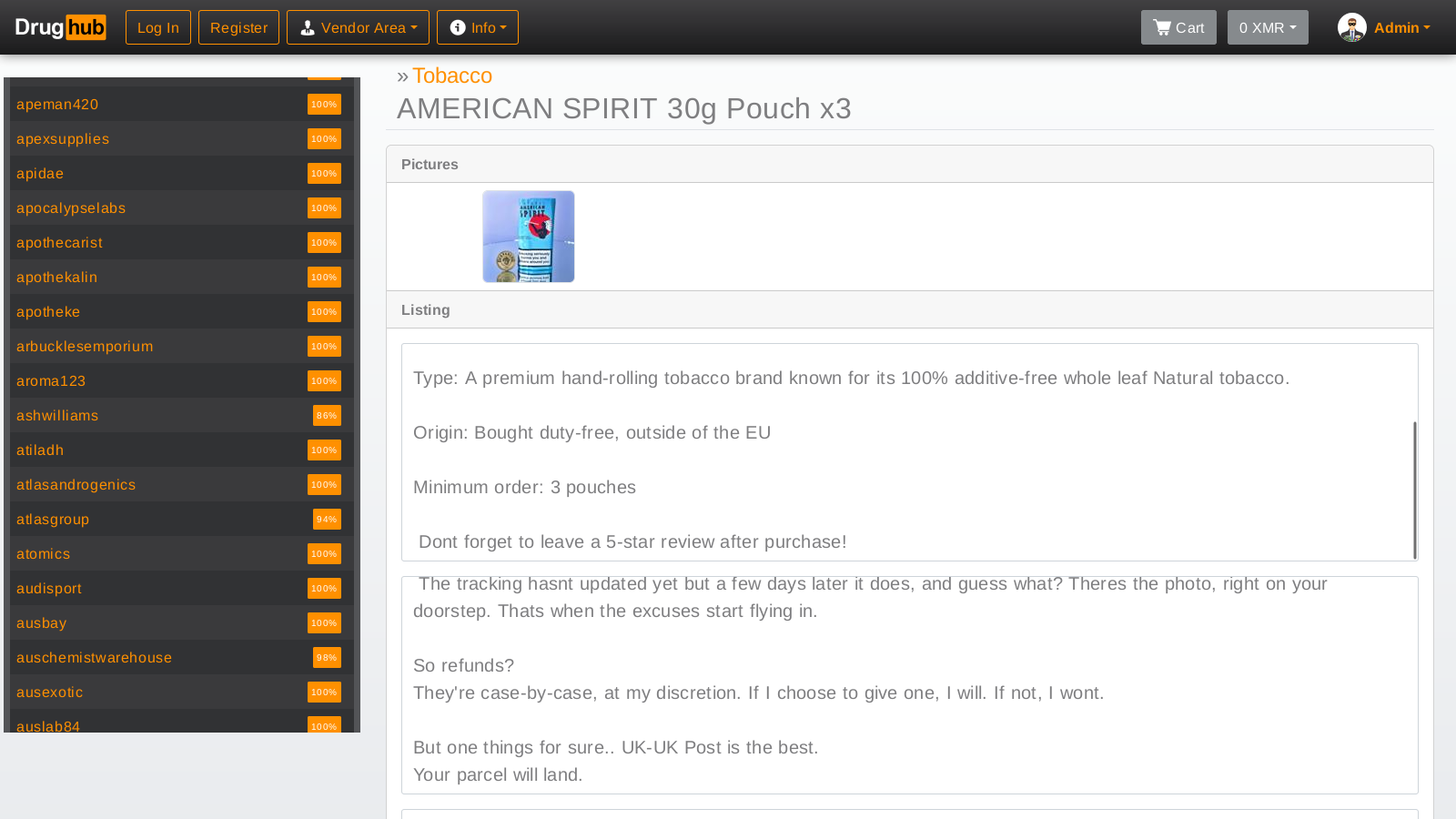
Fig 4. Main Market Dashboard
The centralized layout showcasing statistical categories and UI flow.
Historical Log
Initial Deployment
The core logic was deployed to the Tor network. Early operators prioritized stability testing of the Monero daemon integration and internal escrow logic before widespread indexing.
Security Hardening
In response to network-wide denial-of-service stress, operators implemented a robust proof-of-work mechanism at the entry nodes, significantly lowering infrastructure load.
Walletless Maturation
Full transition to a direct-payment model. Acknowledging the risks of traditional centralized wallets, the architecture adapted to ensure independent merchants and users process funds strictly per order.
Community Dynamics
The sociological framework of the platform revolves around reputation metrics and financial risk delegation. To deter malicious actors, the system heavily regulates who is authorized to distribute goods.
A mandatory non-refundable security bond in XMR is required from all distributors, creating a high cost of entry that neutralizes low-level mass-registration attacks.
A structured dispute protocol acts as an independent arbitrator, relying on cryptographic proof of dispatch and receipt before any funds are released from the multisig holding address.